What is a Zero Day exploit?
The Zero Day Exploit, a recently discovered vulnerability that hackers can use to hack the systems. This vulnerability is very much dangerous since hackers only aware of the Zero Day existence. These Zero Day vulnerability is not being patched or made public. In contrast, others define them as Zero Day attacks that utilize the advantage of a security vulnerability on the same day as the general public came to aware of that publically. Therefore it is termed as Zero Day Exploit or the Zero Day Vulnerability.
Most of the software vulnerabilities discovered by hackers, software vendors, security companies, researchers, or users. If the hackers detect the vulnerability, it will be kept as a secret as long as others are aware of it.
When this vulnerability shared with other hackers, they started to exploit it until the software vendors come out with a patch to fix the flaw in the software. Therefore the vendor of the software has zero days to find a patch for the flaw. Therefore it is called Zero Day vulnerability. However, if the hacker exploits it before the vendor finds a fix, the attack is zero-day. Frequent operating system upgrades, other software upgrades, and changes are another reason for a Zero Day vulnerability.
Zero Day Exploit can be of any form, and it may be a URL redirection or SQL injection, buffer overflows, or any other kind.
The Zero Day Vulnerability Categories:
- The detection based on the signature: Using the available database of malware, and signature as the reference, it is possible to detect the threat.
- Detection based on the behavior: the vulnerability detected based on the malware’s interaction with the existing software.
- Detection based on the available Data: comparing with the previously collected data of exploits to analyze the system behavior.
- Hybrid Detection: It combines all the three techniques to detect the vulnerability.
How to protect yourself from Zero Day Exploit?
You have to follow few things to defend yourself against Zero Day Exploit.
Always keep your system updated and patched to prevent exploitation. Always enable automatic updates so that you may be protected from the Zero Day Exploit. This is our best advise.
Protect your software using the best security solutions that could protect yourself from Zero Day attacks.
Always give priority mails and news from your software vendors about the security measures and patches about any vulnerability.
How to detect Zero Day Exploit?
Nowadays, Zero Day attacks are more refined, and the vendors are witnessing increasing difficulties in identifying and detecting the attacks. Therefore it is crucial to deploy the best security trained team dealing with zero tolerance with the Zero Day attacks.
Segregate responsibilities within the team members to tackle any critical situation. Train your security team with updated latest technology and tools to handle any situation. Always have a contingency plan in case of untoward incidents.
Enhance the in-depth system monitoring like detecting hooks, detecting hidden file processing, kernel, and registry integrity checks; monitoring the user actions can help you discover and protect yourself early. The Zero Day Exploit can be identified, recognizing abnormal behavior of the application program.
How Hackers create Zero Day exploits?
The hackers follow some systematic steps to create the exploits. The exploiters run the attack surface analysis in the preliminary stage. Moreover, Attack surface analysis is nothing but analyzing the source codes and binary codes of the software program.
At this stage, the attacker analyzes the system software by studying it to find legitimate entry to it with his expert skill in the codes and protocols. With the attack surface analysis, one can see the vulnerability.
If this method doesn’t any fruitful results, the attacker will use automated programs to find the Zero Day Vulnerabilities in the system software. The automated programs feed random values to the system and monitor their behavior and find the vulnerabilities very easily.
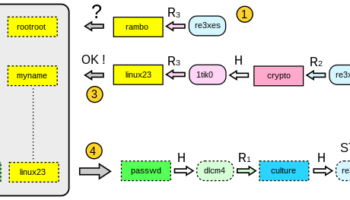
A zero Day Attack
Once they find the vulnerability, they will develop the malware than can be used to hack the system. Since most hackers are experts in practical knowledge, they will easily place a shellcode in the Zero Day vulnerability if the particular exploited system stack target has enough memory. If there is not enough memory, the hacker will inject the codes that will allow the software application to skip to the full shellcode.
The hacker effectively hides the exploit code. The hacker hides the exploit code metamorphically to function identical with the original but not traced easily. Sometimes the hacker uses the sophisticated polymorphic encryption technique to hide the rouge program.
The polymorphic Zero Day exploits are very hard to detect. Once the malware developed, the hacker delivers the malware automatically or in some other methods like phishing or fake download prompts.
Whatever the method of the exploit, different strategies and techniques developed to find them.
Though Zero Day attack prevention and detection are extremely tough, regular software updates and monitoring can reduce the exploit to a considerable amount.
Real-time monitoring and rapid response can control any sophisticated attack.
Points to Ponder:
Zero Day Vulnerability is an innate error in the software or the code; or a flaw in the way one software interacts with the other software that the vendor has not yet discovered.
Zero Day Exploit is an act of misusing the Zero Day Vulnerability to gain access to the target and misusing it
A zero day attack is an act of using Zero Day Exploit for hacking purposes. The Zero Day attack happens when the intruder is misusing the vulnerability currently unknown to the user or the software vendor.