Thrusters Designed With Ferrofluid to Push Satellites into the Orbit
The space exploration will never be the same again with the developed of a new thruster model which is better and aggressive at work than anything available today. This thruster makes use of the ionic liquid ferrofluid which is great for the task of propelling small satellites to the space.
This liquid has been developed by a doctoral candidate named Brandon Jackson from the Michigan Technological University. The computational model designed by Jackson has shown the capability of this liquid which has the characteristic of spiking.It shouldn’t come as a surprise that more than1300 active satellites are there in the earth’s orbit. The size of the satellites ranges from the shoebox or Smartphone to a small school bus. The current advancement in the satellite and computational system has made it possible to build such small satellite which can perform all the functions which are usually done by the large satellites.
Secondly it has been found that maneuvering small satellites are quite easier, quicker and efficient than the large ones. The method devised by Jackson of the electro spray will be great for propelling the small satellites into the space.
The advantages of using the Ferrofluids
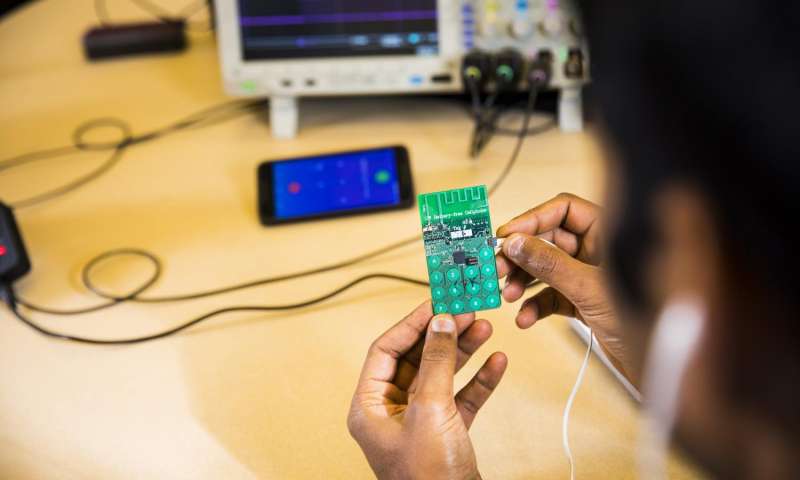
Two prominent professors at Michigan Tech namely L. Brad King and Elaine Starr has been successful a new kind of micro thruster which has the ability to assemble on its won from the propellant when it enters in the magnetic field. The best thing about this tiny thruster is that it doesn’t need fragile needles and happens to be essentially indestructible.
How Ferrofluids works?
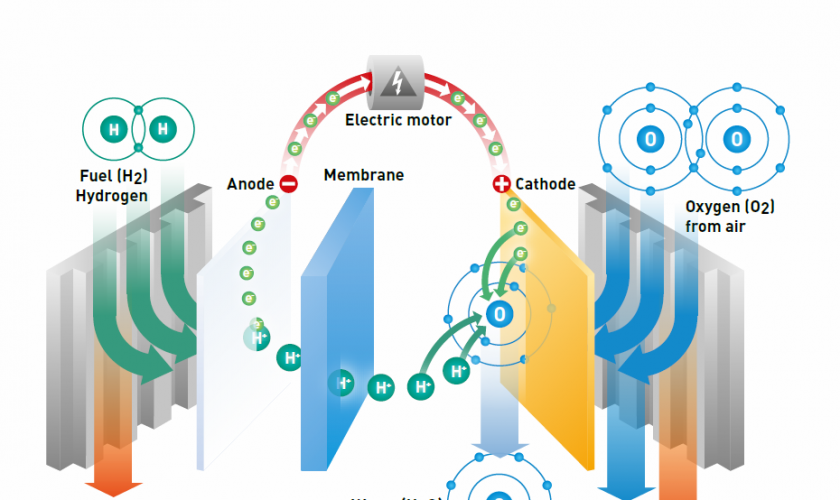
King has shown that making use of Jackson’s iconic liquid ferrofluid that they had been able to build a powerful thruster for the small satellites.
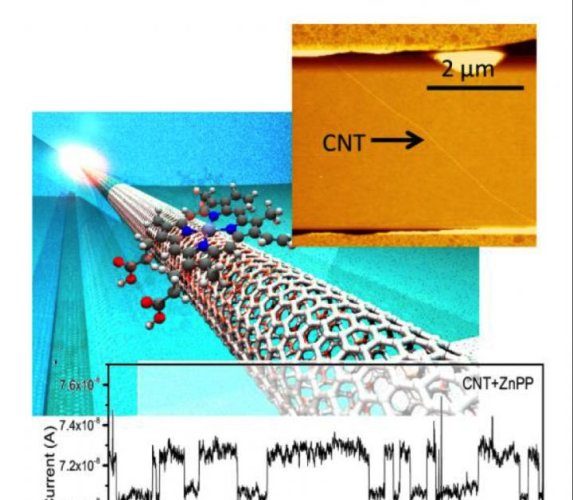
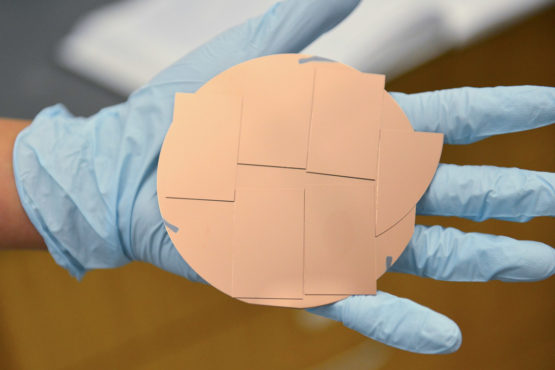
When a metal is put underneath a small cup of ferrofluid then it results in creating a beautiful hedgehog structure of the aligned peaks which is quite breathtaking to look at. Later in their research it was found that by simply applying a stronger electric field helps in bringing an array of peaks and it was found that each one of peak emits quite a large sum of micro-jet of ions.
This specifically happens due to the Risenweig instability and in this experiment it is also seen that peak tends to heal them as well as regrow in case it is damaged.
The research on Ferrofluids will go on
In order to boost the study in the physics of the ferrofluids the AFOSR has awarded the King a second contract. King has stressed that they had learned a lot from the liquid and so far they had focused their efforts on modeling a single but now they will be scaling up their research towards modeling multiple peaks.
Now they will be bring new set of experiments on developing working thruster but it should be noted that such thruster are still years away from becoming a reality. The biggest challenge for the team will be to make 100 peaks and above and each of it having identical thrust.